A Comprehensive Guide to Network Segmentation
Learn how network segmentation enhances security, minimizes cyber threats, and improves network performance. Discover best practices, tools, and implementation strategies.
5/20/202510 min read


Introduction
With cyberattacks becoming more sophisticated, network segmentation has emerged as a critical cybersecurity strategy for businesses. It involves dividing a network into isolated segments to reduce attack surfaces, contain breaches, and optimize performance. According to IBM’s Cost of a Data Breach Report, companies using network segmentation reduce breach costs by 35% compared to unsegmented networks.
As organizations increasingly rely on cloud computing, IoT devices, and remote work, implementing strong network segmentation policies is essential to prevent lateral movement of threats and protect sensitive data. This guide provides a detailed breakdown of network segmentation, including its benefits, tools, best practices, and step-by-step implementation.
Table of Contents
What is Network Segmentation?
Why Network Segmentation is Important
Best Tools for Network Segmentation
How to Choose the Right Network Segmentation Solution
Step-by-Step Guide to Implementing Network Segmentation
FAQs About Network Segmentation
1. What is Network Segmentation?
Network segmentation is a security practice that involves dividing a computer network into smaller, isolated sub-networks or zones. This approach limits unrestricted access, ensuring that only authorized users and devices can communicate within specific network segments.
There are three primary types of network segmentation:
Physical Segmentation – Uses separate hardware and network infrastructure to isolate different segments.
Logical Segmentation – Utilizes VLANs (Virtual Local Area Networks) and firewalls to create access controls without needing additional physical infrastructure.
Microsegmentation – Enforces security policies at an application or workload level, often using zero-trust security models.
Defining Network Segmentation
Network segmentation is a cybersecurity strategy that involves dividing a larger network into smaller, isolated segments to enhance security, control, and performance. By doing so, organizations can enforce strict access controls, ensuring that only authorized users and devices can communicate within specific segments.
Without segmentation, cybercriminals who infiltrate a network can move laterally, gaining unrestricted access to sensitive data, critical infrastructure, and essential applications. However, with proper segmentation in place, even if an attacker breaches one part of the network, they are effectively contained within that segment, minimizing potential damage.
Types of Network Segmentation
Organizations implement segmentation in different ways, depending on their security and operational requirements. The three primary types include:
Physical Segmentation – Uses separate network hardware (routers, switches, and dedicated firewalls) to create physically isolated networks, often employed in highly secure environments.
Logical Segmentation – Uses Virtual Local Area Networks (VLANs) and firewall rules to segment traffic within the same physical infrastructure, allowing for flexibility while maintaining security.
Microsegmentation – A more granular approach that enforces individualized security policies at the workload or application level, commonly used in cloud and hybrid environments.
How Network Segmentation Works
At its core, network segmentation is about controlling traffic flow between different areas of a network. Organizations use firewalls, intrusion prevention systems (IPS), and identity-based access controls to establish rules governing which users, devices, or applications can communicate across network segments.
For example, in a segmented network:
Guest Wi-Fi networks remain separate from internal corporate systems.
HR and finance databases are isolated from general employee access.
Operational Technology (OT) systems in manufacturing plants are segmented to prevent cyber threats from reaching industrial controls.
Benefits of Network Segmentation
🔹 Minimized Attack Surfaces – Limits the spread of malware, ransomware, and unauthorized access.
🔹 Improved Access Control – Ensures that employees, contractors, and third-party vendors only access the data and systems necessary for their roles.
🔹 Regulatory Compliance – Meets HIPAA, PCI-DSS, and GDPR requirements by enforcing strict security controls and reducing data breach risks.
🔹 Optimized Network Performance – Reduces congestion and isolates mission-critical applications from unnecessary traffic.
🔹 Zero Trust Security Alignment – Works alongside Zero Trust Network Access (ZTNA) by enforcing continuous verification and least privilege access policies.
By implementing effective network segmentation strategies, organizations can significantly enhance their cyber resilience, regulatory compliance, and network efficiency.
2. Why Network Segmentation is Important
1. Strengthens Cybersecurity
Network segmentation is a proven defense mechanism against cyber threats, malware, and ransomware attacks. By limiting unrestricted lateral movement, segmentation ensures that even if a breach occurs, attackers cannot easily compromise the entire network. This containment strategy significantly reduces potential damage and prevents unauthorized access to critical data.
Example: In 2023, a global financial institution was hit by a ransomware attack. However, due to proper network segmentation, the attack was contained within a single business unit, preventing it from spreading to mission-critical banking systems.
2. Ensures Compliance with Industry Standards
Businesses handling sensitive customer data must comply with regulatory frameworks like:
HIPAA (for healthcare organizations)
PCI-DSS (for financial institutions processing credit card transactions)
GDPR (for data protection and privacy in Europe)
Network segmentation helps organizations enforce strict access control, ensuring that sensitive information is only accessible to authorized personnel, reducing data breach risks and regulatory fines.
📌 Example: A retail company implementing network segmentation successfully passed PCI-DSS audits, as customer payment data was isolated from general business operations, reducing risk exposure.
3. Improves Network Performance and Reduces Congestion
Dividing a network into smaller, manageable segments prevents network congestion, improves bandwidth allocation, and ensures that high-priority applications (such as cloud storage, VoIP services, or financial transactions) are not slowed down by unnecessary traffic.
📌 Example: A large enterprise using VLAN segmentation reported a 25% improvement in network speed and lower latency for cloud-based applications, increasing productivity across global offices.
4. Reduces Insider Threat Risks
One of the most overlooked cybersecurity risks comes from insider threats—employees, contractors, or business partners who may intentionally or unintentionally compromise security. By enforcing least privilege access through network segmentation, businesses can ensure that users only access the data and systems necessary for their job functions.
📌 Example: In 2022, a disgruntled employee at a healthcare facility attempted to leak confidential patient data. However, since the facility had network segmentation policies in place, the employee was restricted from accessing sensitive medical databases, preventing a data breach.
5. Protects Against IoT and Third-Party Risks
With the rapid adoption of Internet of Things (IoT) devices, businesses are more vulnerable to cyberattacks than ever before. Many IoT devices operate with default passwords and limited security controls, making them prime targets for hackers. By segmenting IoT networks from enterprise systems, organizations can reduce the risk of botnet attacks and unauthorized access.
📌 Example: A smart manufacturing plant segmented its industrial IoT (IIoT) devices from its corporate network, preventing hackers from exploiting vulnerabilities in IoT sensors to access critical infrastructure.
Final Thoughts on the Importance of Network Segmentation
The modern threat landscape demands proactive security strategies, and network segmentation remains one of the most effective ways to prevent breaches, reduce cyber risk, and optimize network performance. Whether you're securing financial data, healthcare records, or cloud-based applications, segmentation is a vital cybersecurity measure that every organization should implement.
3. Best Tools for Network Segmentation
Why You Need Network Segmentation Tools
Effective network segmentation requires specialized tools to enforce access controls, manage policies, monitor traffic, and respond to security threats. The best segmentation tools integrate with firewalls, intrusion prevention systems (IPS), and cloud security solutions to create a multi-layered defense strategy. Businesses implementing these tools gain:
✅ Enhanced security by preventing lateral movement of cyber threats.
✅ Simplified compliance with regulations like HIPAA, PCI-DSS, and GDPR.
✅ Improved network performance by reducing congestion and isolating traffic.
✅ Scalability to manage segmentation across on-premise, hybrid, and cloud networks.
Top Network Segmentation Tools
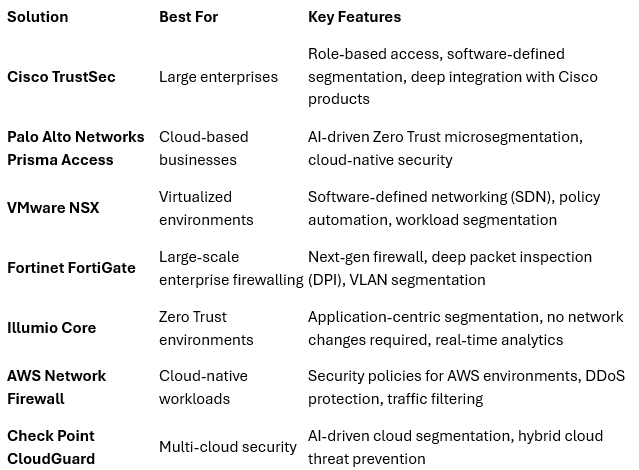
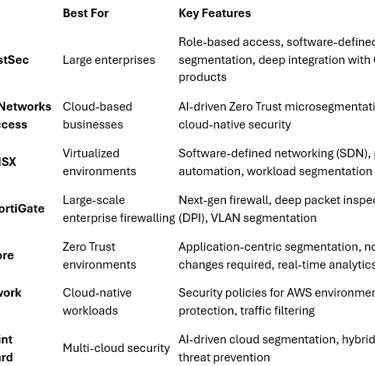
Here are some of the best tools for network segmentation, ranging from firewall-based solutions to advanced microsegmentation platforms:
1. Cisco TrustSec
🔹 Best for: Enterprise-grade policy-based segmentation.
🔹 Features:
Dynamic role-based access control (RBAC).
Enforces software-defined segmentation.
Integrates with Cisco’s security ecosystem.
🔹 Why Use It? Cisco TrustSec simplifies segmentation by automating security policies and reducing reliance on VLANs and IP-based controls.
2. Palo Alto Networks Prisma Access
🔹 Best for: Cloud-based microsegmentation and Zero Trust security.
🔹 Features:
Identity-based segmentation with Zero Trust controls.
Protects hybrid and multi-cloud networks.
AI-driven threat detection and response.
🔹 Why Use It? Ideal for cloud-first businesses looking for scalable, AI-driven security segmentation.
3. VMware NSX
🔹 Best for: Software-defined networking (SDN) and microsegmentation.
🔹 Features:
Application-level segmentation for granular security.
Automated policy enforcement based on workloads.
Network visualization for monitoring and analytics.
🔹 Why Use It? VMware NSX is a top choice for organizations using virtualized environments and cloud-based infrastructures.
4. Fortinet FortiGate
🔹 Best for: Firewall-based segmentation for large enterprises.
🔹 Features:
Next-generation firewall (NGFW) with built-in segmentation.
Deep packet inspection (DPI) to detect and block threats.
Supports VLAN segmentation for isolated network zones.
🔹 Why Use It? FortiGate is an all-in-one security solution that provides firewall protection, IPS, and segmentation.
5. Illumio Core
🔹 Best for: Zero Trust microsegmentation in hybrid environments.
🔹 Features:
Application-centric segmentation with real-time analytics.
Blocks lateral movement of malware and ransomware.
No network changes required for deployment.
🔹 Why Use It? Illumio Core provides unmatched visibility and control, making it a great choice for Zero Trust security architectures.
6. AWS Network Firewall & Security Groups
🔹 Best for: Cloud-native segmentation for AWS workloads.
🔹 Features:
Stateful firewall policies for securing cloud resources.
Security group rules to restrict access within AWS environments.
Integration with AWS Shield for DDoS protection.
🔹 Why Use It? AWS Network Firewall enables secure cloud segmentation, preventing unauthorized access within AWS-hosted applications.
7. Check Point CloudGuard
🔹 Best for: Cloud security and network segmentation.
🔹 Features:
AI-driven threat intelligence for cloud segmentation.
Protects hybrid cloud networks from cyber threats.
Automated zero-trust security enforcement.
🔹 Why Use It? CloudGuard provides multi-cloud visibility and protection, perfect for businesses operating across AWS, Azure, and Google Cloud.
How to Select the Best Network Segmentation Tool
When choosing a network segmentation solution, consider the following:
✅ Business Size & Infrastructure – Large enterprises may benefit from Cisco TrustSec or Fortinet FortiGate, while cloud-based businesses might prefer Palo Alto Prisma Access or AWS Network Firewall.
✅ Security Compliance Needs – Organizations handling financial transactions (PCI-DSS) or healthcare data (HIPAA) should prioritize Illumio Core, Fortinet, or Check Point CloudGuard.
✅ Ease of Integration – VMware NSX is ideal for virtualized environments, while AWS Network Firewall seamlessly integrates with AWS cloud resources.
✅ Zero Trust Capabilities – If you’re adopting Zero Trust segmentation, tools like Illumio Core and Palo Alto Prisma Access are highly effective.
4. How to Choose the Right Network Segmentation Solution
Choosing the right network segmentation solution is critical to ensuring strong security, compliance, and network efficiency. With a wide range of tools available, businesses must evaluate solutions based on infrastructure requirements, security policies, scalability, and cost-effectiveness.
Key Factors to Consider When Selecting a Network Segmentation Solution
🔹 Business Size and Infrastructure – Whether you are a small business, mid-sized enterprise, or large corporation, the segmentation solution should align with your existing network architecture and growth plans.
🔹 Security and Compliance Needs – Organizations in regulated industries such as finance, healthcare, and government must choose solutions that support PCI-DSS, HIPAA, and GDPR compliance through fine-grained access control and data protection policies.
🔹 Cloud vs. On-Premise vs. Hybrid Compatibility – If your business operates in multi-cloud, hybrid, or on-premise environments, selecting a solution that seamlessly integrates across all infrastructures is essential.
🔹 Zero Trust Capabilities – Implementing Zero Trust Network Access (ZTNA) requires segmentation tools that enforce continuous authentication, microsegmentation, and least privilege access controls.
🔹 Ease of Deployment and Management – A good segmentation solution should offer automation, AI-driven analytics, and centralized visibility to streamline network administration.
🔹 Performance Impact – Some segmentation tools can create latency issues or bottlenecks if not optimized correctly. Choosing high-performance solutions with low network overhead is essential.
Comparison of Network Segmentation Solutions
Step-by-Step Guide to Choosing the Right Segmentation Tool
Step 1: Assess Your Security and Compliance Requirements
Identify the type of sensitive data your business handles.
Ensure the solution aligns with industry compliance mandates such as NIST, HIPAA, or PCI-DSS.
Choose a tool that provides auditing, access logs, and policy enforcement to meet security standards.
Step 2: Evaluate Network Architecture
Determine whether your organization requires physical, logical, or microsegmentation.
Identify whether the tool integrates with on-premise, hybrid, or cloud environments.
Consider solutions that support multi-cloud compatibility if operating in AWS, Azure, or Google Cloud.
Step 3: Prioritize Zero Trust Capabilities
Select a tool that enforces identity-based segmentation and prevents lateral movement of cyber threats.
Ensure the solution supports multi-factor authentication (MFA) and least privilege access policies.
Step 4: Consider Automation and AI-Driven Security
Look for segmentation solutions that offer AI-based threat detection, behavioral analytics, and automated policy enforcement.
AI-driven tools reduce manual intervention and provide real-time visibility into security risks.
Step 5: Test Performance and Scalability
Conduct a proof of concept (PoC) to evaluate how the tool affects network performance.
Ensure the solution can scale as your business expands without creating network bottlenecks.
Choose tools that support high-speed network traffic filtering and segmentation.
Step 6: Compare Cost and ROI
Consider both initial costs and ongoing maintenance expenses.
Evaluate the return on investment (ROI) based on security improvements, reduced breach risks, and compliance benefits.
5. Step-by-Step Guide to Implementing Network Segmentation
Implementing network segmentation effectively requires a structured approach that aligns with security best practices, business needs, and compliance requirements. Below is a detailed, step-by-step guide to help businesses deploy segmentation while maximizing security and performance.
Step 1: Conduct a Network Audit
Before implementing segmentation, you must assess your current network infrastructure to identify potential security gaps, high-risk areas, and critical assets.
✅ Map out all network components – Identify servers, endpoints, IoT devices, cloud resources, and third-party connections.
✅ Classify data and assets by sensitivity level – Determine which systems require higher security controls (e.g., financial databases, medical records, intellectual property storage).
✅ Analyze current network traffic flow – Understand how data moves between different departments, applications, and cloud services to ensure optimal segmentation policies.
✅ Identify security vulnerabilities – Check for weak authentication, unpatched systems, and excessive user permissions that could create security risks.
🔹 Tool Recommendation: Use network monitoring solutions like Wireshark, SolarWinds, or Cisco DNA Center to analyze network traffic and detect vulnerabilities.
Step 2: Define Segmentation Policies and Access Controls
Once you’ve audited the network, establish clear segmentation policies to dictate how different parts of the network interact.
✅ Adopt the Least Privilege Principle (LPA) – Ensure that only authorized users and devices have access to specific network segments.
✅ Define role-based access control (RBAC) – Assign access permissions based on employee roles and job functions.
✅ Segment critical business functions – Separate networks for finance, HR, R&D, and IT security teams to minimize risk exposure.
✅ Restrict IoT and guest networks – Ensure IoT devices, vendors, and guest Wi-Fi are isolated from core business systems.
🔹 Security Best Practice: Implement Zero Trust Network Access (ZTNA) to enforce continuous verification and adaptive access controls.
Step 3: Implement Network Segmentation Using VLANs, Firewalls, and Microsegmentation
After defining segmentation policies, apply them using network security technologies.
✅ Use VLANs (Virtual Local Area Networks) – VLANs separate network traffic logically, preventing unauthorized access between departments.
✅ Deploy Next-Gen Firewalls (NGFWs) – Firewalls such as Fortinet FortiGate, Palo Alto Networks, or Cisco ASA help enforce policy-based segmentation.
✅ Apply Microsegmentation for Cloud and Hybrid Environments – Use solutions like VMware NSX, Illumio Core, or Palo Alto Prisma to apply granular security policies within cloud workloads and applications.
✅ Utilize Intrusion Prevention Systems (IPS) – IPS solutions detect and block unauthorized attempts to cross-segment boundaries.
🔹 Example: A financial institution might segment ATM networks, internal payment processing, and cloud-based services to prevent hackers from moving across systems.
Step 4: Implement Network Monitoring and Threat Detection
✅ Enable real-time monitoring – Use AI-driven security analytics like Splunk, IBM QRadar, or Darktrace to detect anomalous traffic behavior.
✅ Deploy Security Information and Event Management (SIEM) systems – SIEM tools correlate security events to identify segmentation violations.
✅ Use automated alerts and response mechanisms – Tools like Microsoft Defender for Endpoint or FireEye Helix can automatically block malicious network activities.
🔹 Example: A cloud-based enterprise uses SIEM alerts to detect unauthorized access attempts to segmented data centers, triggering automated firewall adjustments.
Step 5: Test and Validate Segmentation Policies
✅ Conduct penetration testing – Hire ethical hackers or use automated testing tools to ensure segmentation rules cannot be bypassed.
✅ Perform security audits – Regularly review segmentation logs, firewall rules, and access controls to verify compliance.
✅ Simulate real-world attack scenarios – Run red team exercises to test how well your segmentation policies block cyber threats.
🔹 Best Practice: Use penetration testing tools like Metasploit, Nessus, or Qualys to simulate attacks and evaluate segmentation defenses.
Step 6: Continuously Optimize and Update Segmentation Strategies
✅ Review policies regularly – Security landscapes evolve; update segmentation rules every 6-12 months.
✅ Automate policy enforcement – Use AI-based security orchestration solutions to dynamically adjust segmentation based on real-time threat intelligence.
✅ Train employees on segmentation best practices – Ensure IT and security teams understand segmentation policies, Zero Trust principles, and incident response plans.
🔹 Example: A healthcare organization updates segmentation rules quarterly to adapt to evolving HIPAA compliance regulations and emerging ransomware threats.
Final Thoughts on Implementing Network Segmentation
Deploying network segmentation requires careful planning, strong security policies, and continuous monitoring to remain effective. By segmenting critical assets, applying Zero Trust principles, and leveraging AI-driven security solutions, organizations can reduce cyber risks, enhance regulatory compliance, and optimize network performance.