Best Practices for Data Encryption
Discover the best practices for data encryption to safeguard sensitive information, protect against cyber threats, and ensure compliance with global security regulations.
10/23/202412 min read


Introduction
Data encryption is one of the most effective ways to protect sensitive information from unauthorized access, breaches, and cyber threats. With cybercrime damages projected to reach $10.5 trillion annually by 2025, encryption has become a critical element of modern cybersecurity strategies. According to IBM’s Cost of a Data Breach Report 2023, the average cost of a data breach reached $4.45 million, making encryption a necessary defense mechanism for businesses of all sizes.
A 2022 study by Cybersecurity Ventures found that over 80% of enterprises experienced a cyberattack involving data exposure, with unencrypted data being among the most compromised assets. Additionally, with 90% of businesses moving to cloud-based services, encrypting data in storage, transit, and use is paramount to ensuring security and compliance.
From financial institutions to healthcare providers, businesses across industries must encrypt data to prevent identity theft, corporate espionage, and regulatory violations. Governments worldwide are also mandating stricter encryption policies under regulations like GDPR, HIPAA, and PCI-DSS. Without proper encryption strategies, organizations risk not only financial losses but also reputational damage and loss of customer trust.
This article explores the best practices for data encryption, its importance, recommended tools, and a step-by-step guide to implementation.
Data encryption is one of the most effective ways to protect sensitive information from unauthorized access, breaches, and cyber threats. With cybercrime damages projected to reach $10.5 trillion annually by 2025, encryption has become a critical element of modern cybersecurity strategies. From financial institutions to healthcare providers, businesses across industries must encrypt data to prevent identity theft, corporate espionage, and compliance violations.
This article explores the best practices for data encryption, its importance, recommended tools, and a step-by-step guide to implementation.
Table of Contents
What is Data Encryption?
Why is Data Encryption Important?
Best Encryption Tools & Certifications
How to Choose the Right Encryption Solution
Step-by-Step Guide to Implementing Data Encryption
FAQs About Data Encryption
What is Data Encryption?
Data encryption is the process of transforming readable data (plaintext) into an unreadable format (ciphertext) using cryptographic algorithms. This ensures that only authorized parties with the correct decryption key can access the original data, safeguarding it from unauthorized access, cyber threats, and data breaches.
How Does Data Encryption Work?
Encryption works by using an encryption algorithm and a cryptographic key to scramble data into an unreadable format. The data can only be restored to its original form by applying the correct decryption key. The strength of encryption depends on the algorithm used and the length of the encryption key—longer keys generally provide stronger security.
Real-World Examples of Data Encryption
Personal Use: When you send a message via WhatsApp or Signal, it is encrypted end-to-end, meaning only the sender and recipient can read it.
Enterprise Security: Banks use encryption to protect customer financial transactions and sensitive account data from cybercriminals.
Healthcare Data Protection: Hospitals encrypt patient records to comply with regulations like HIPAA and prevent unauthorized access to medical information.
Types of Encryption
Symmetric Encryption:
Uses a single key for both encryption and decryption.
Example: AES (Advanced Encryption Standard) 256-bit, widely used for securing sensitive data.
Pros: Faster encryption and decryption.
Cons: Requires secure key management since the same key must be shared between sender and recipient.
Asymmetric Encryption:
Uses a public key for encryption and a private key for decryption.
Example: RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography), commonly used in SSL/TLS for securing online communications.
Pros: More secure than symmetric encryption since private keys do not need to be shared.
Cons: Slower due to complex mathematical computations.
Hashing (One-Way Encryption):
Converts data into a unique fixed-length value that cannot be decrypted.
Example: SHA-256 (Secure Hash Algorithm) is widely used for password storage and blockchain security.
Pros: Ideal for ensuring data integrity and authentication.
Cons: Cannot be reversed, making it unsuitable for encrypting data that needs to be recovered.
Encryption in Different Contexts
Data at Rest: Encrypting stored files and databases (e.g., full-disk encryption, encrypted backups).
Data in Transit: Securing data as it moves across networks (e.g., HTTPS, VPN encryption, email encryption).
Data in Use: Protecting data while it is actively being processed or used in applications.
By implementing encryption at all levels, organizations and individuals can effectively safeguard their sensitive information from cyber threats and unauthorized access.
Data encryption is the process of converting plaintext information into unreadable ciphertext using cryptographic algorithms. This ensures that only authorized users with the correct decryption key can access the data. Encryption is used to secure data at rest, in transit, and in use across various digital environments.
Types of Encryption
Symmetric Encryption: Uses a single key for both encryption and decryption (e.g., AES-256).
Asymmetric Encryption: Uses a public key for encryption and a private key for decryption (e.g., RSA, ECC).
Hashing: A one-way encryption method used for verifying data integrity (e.g., SHA-256).
Why is Data Encryption Important?
Data encryption is a fundamental cybersecurity measure that protects sensitive information from unauthorized access, cyber threats, and regulatory non-compliance. As digital data usage expands, so does the risk of breaches, making encryption a necessity rather than an option.
1. Prevents Data Breaches and Cyberattacks
Encryption ensures that even if attackers gain access to stored or transmitted data, they cannot read it without the decryption key.
Case Study: In 2017, Equifax suffered a massive data breach affecting 147 million individuals. Had stronger encryption measures been implemented, the stolen personal data could have remained unreadable and useless to hackers.
2. Ensures Compliance with Security Regulations
Many global regulations, including GDPR, HIPAA, PCI-DSS, and CCPA, mandate encryption to protect sensitive data.
Failure to comply can result in severe penalties, legal liabilities, and reputational damage.
Example: Under GDPR, companies that fail to properly encrypt personal data risk fines of up to €20 million or 4% of their global revenue—whichever is higher.
3. Protects Intellectual Property and Business Confidentiality
Organizations handle confidential information such as trade secrets, financial records, and proprietary data.
Encryption safeguards this information from competitors, insider threats, and corporate espionage.
Example: A major manufacturing firm encrypts its research and development data to prevent leaks that could compromise its competitive advantage.
4. Enhances Consumer Trust and Brand Reputation
Customers are more likely to trust businesses that demonstrate strong data protection measures.
Encrypted communication platforms like WhatsApp and Signal attract users due to their emphasis on privacy.
Example: Companies in e-commerce and fintech prioritize encrypted payment processing to assure customers their financial transactions are secure.
5. Reduces the Risk of Financial Loss
The average cost of a data breach in 2023 was $4.45 million, according to IBM’s Cost of a Data Breach Report.
Encryption minimizes financial damages by reducing liability, limiting the impact of breaches, and protecting against fraud.
Example: Financial institutions encrypt customer banking data to prevent unauthorized transactions and fraud.
6. Protects Data Across Multiple Environments
Encryption ensures data security at rest, in transit, and in use:
At Rest: Protects stored data on servers, databases, and hard drives.
In Transit: Secures data as it moves across networks, including emails and web communications.
In Use: Prevents unauthorized access while data is actively being processed.
Example: Cloud storage providers use encryption to secure user data, ensuring that even if the cloud service is compromised, the data remains unreadable without the proper credentials.
7. Strengthens Identity Protection
Encryption is widely used in authentication processes, including password hashing and digital certificates.
Protects personally identifiable information (PII), such as Social Security numbers, medical records, and financial details.
Example: Secure online banking systems use encrypted authentication to verify customer identities and prevent phishing attacks.
Final Thought
With cyber threats evolving rapidly, data encryption remains one of the most effective ways to secure sensitive information and prevent costly breaches. Implementing strong encryption policies not only enhances security but also ensures regulatory compliance and fosters consumer confidence in an organization’s ability to protect data.
Best Encryption Tools & Certifications
Choosing the right encryption tools and certifications is critical to safeguarding sensitive data from cyber threats and ensuring compliance with security regulations. With numerous options available, businesses must carefully evaluate solutions based on their specific needs.
Key Considerations Before Selecting an Encryption Tool
Before implementing an encryption solution, consider the following factors to ensure that it aligns with your organization's security and operational needs:
Type of Data to Protect:
Identify whether the encryption is needed for data at rest (stored data), data in transit (network communication), or data in use (actively processed data).
Highly sensitive data, such as financial transactions or medical records, requires stronger encryption algorithms like AES-256.
Compliance and Regulatory Requirements:
Ensure the encryption tool meets industry-specific standards such as GDPR, HIPAA, PCI-DSS, CCPA, or FedRAMP.
Some industries require additional layers of security, including hardware security modules (HSMs) and encryption key lifecycle management.
Integration with Existing Infrastructure:
Select an encryption tool that seamlessly integrates with cloud environments (AWS, Azure, Google Cloud), databases, email systems, and endpoint security solutions.
Ensure compatibility with operating systems, enterprise resource planning (ERP) systems, and cybersecurity frameworks.
Performance Impact:
Some encryption solutions can slow down system performance, especially for large datasets or real-time applications.
Opt for tools with hardware acceleration to minimize processing overhead while maintaining strong encryption.
Encryption Key Management:
Secure storage and management of encryption keys are essential to prevent unauthorized decryption.
Consider solutions with key rotation policies, multi-factor authentication (MFA) for access, and cloud-based key management services.
Ease of Use & Scalability:
Choose a solution that is user-friendly for IT teams while being scalable to accommodate future business growth.
Enterprise-grade encryption solutions should support centralized management, automated updates, and remote configuration.
Cost Considerations:
Encryption tools range from free open-source solutions to enterprise-grade platforms with premium pricing.
Assess whether the pricing model fits your organization's budget, considering factors such as per-user licensing, per-device pricing, or cloud-based subscription fees.
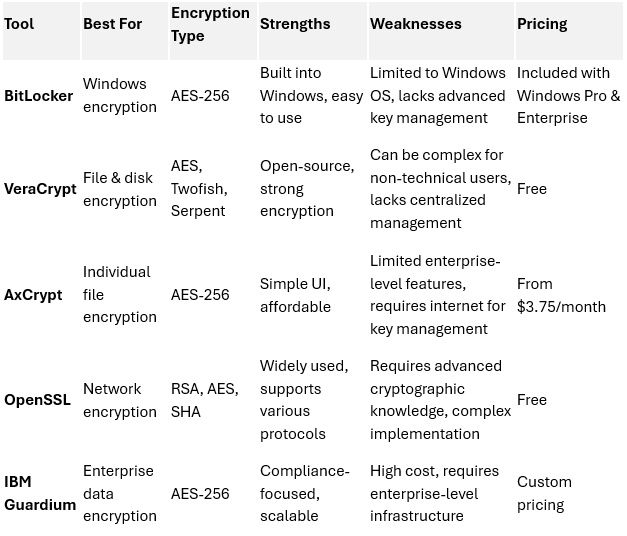
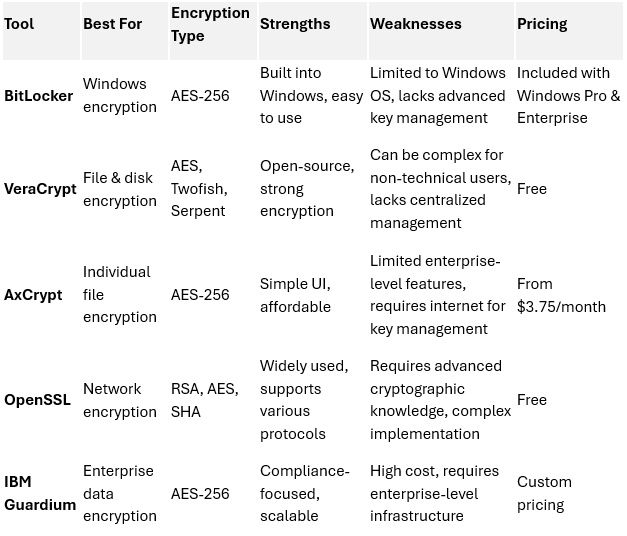
With these considerations in mind, the following table outlines some of the best encryption tools and certifications available today:
Selecting the right encryption tools and certifications is essential for robust security. Here are some of the best options available:
Best Encryption Tools
How to Choose the Right Encryption Solution
Selecting the right encryption solution is crucial for protecting sensitive data while maintaining operational efficiency. Since different organizations have varying security needs, it's essential to evaluate encryption solutions based on key factors, including data sensitivity, compliance requirements, scalability, and integration with existing infrastructure.
Key Considerations When Choosing an Encryption Solution
1. Identify Data Sensitivity & Classification
Determine which types of data require encryption: customer information, financial records, intellectual property, passwords, or regulatory-sensitive data.
Classify data into categories based on risk level (e.g., public, internal, confidential, or highly sensitive) to prioritize encryption efforts.
Example: A healthcare provider must encrypt electronic health records (EHRs) to comply with HIPAA, whereas an e-commerce business must focus on securing customer payment data under PCI-DSS.
2. Ensure Compliance with Industry Regulations
Different industries are subject to varying encryption requirements. Choose a solution that meets the necessary legal and regulatory standards:
GDPR – Requires encryption for protecting personal data.
HIPAA – Mandates encryption for medical records and patient information.
PCI-DSS – Ensures payment card data is encrypted during storage and transmission.
CCPA – Regulates consumer data privacy and encryption requirements.
Tip: Use encryption solutions that generate audit logs and compliance reports to streamline regulatory adherence.
3. Evaluate Encryption Strength & Algorithms
Choose solutions that utilize strong encryption standards, such as:
AES-256 (Advanced Encryption Standard): Gold standard for data protection.
RSA (Rivest-Shamir-Adleman): Common for public-key encryption (used in SSL/TLS security).
ECC (Elliptic Curve Cryptography): Efficient and secure encryption for mobile and cloud applications.
Caution: Avoid outdated encryption methods such as DES (Data Encryption Standard) or weak hashing algorithms like MD5.
4. Assess Integration with Existing Infrastructure
Ensure the encryption solution integrates seamlessly with your existing:
Cloud environments (AWS, Azure, Google Cloud)
Enterprise applications (ERP, CRM, databases)
Email, file storage, and endpoint security solutions
Tip: Choose encryption solutions with API support and automation capabilities to reduce manual security management.
5. Consider Performance & System Impact
Some encryption methods can slow down system performance, particularly for real-time applications and large-scale data encryption.
Tip: Opt for encryption tools that support hardware acceleration (e.g., AES-NI in Intel processors) to maintain system performance.
Caution: Encryption without optimization can lead to increased processing times and negatively affect user experience.
6. Evaluate Key Management Capabilities
Secure encryption key management is vital for preventing unauthorized access.
Look for solutions that offer:
Automated key rotation policies
Multi-Factor Authentication (MFA) for access control
Cloud-based key management services (AWS KMS, Google Cloud KMS)
Caution: Poor key management increases the risk of data exposure, even if encryption is implemented correctly.
7. Determine Scalability & Future Expansion
Choose an encryption solution that scales with your business growth and increasing security needs.
Tip: Cloud-based encryption services offer flexibility and auto-scaling to handle expanding workloads.
Example: An organization that moves from on-premise data storage to the cloud should consider hybrid encryption models that support both environments.
8. Compare Cost & Licensing Options
Encryption solutions vary in cost based on licensing, storage capacity, and deployment model.
Consider pricing structures such as:
Free/Open-source solutions (e.g., VeraCrypt, OpenSSL) for basic encryption needs.
Subscription-based cloud encryption services for enterprise data protection.
Custom enterprise-level encryption suites with full compliance and security management.
Tip: Factor in long-term maintenance costs, including updates, support, and scalability.
Final Thought
Choosing the right encryption solution requires balancing security, compliance, performance, and cost considerations. By thoroughly assessing encryption strength, key management, regulatory compliance, and integration capabilities, organizations can select a robust encryption strategy that aligns with their data protection goals.
When selecting an encryption solution, consider these factors:
Data Sensitivity: Encrypt highly sensitive data using strong algorithms like AES-256.
Compliance Needs: Ensure the solution meets GDPR, HIPAA, PCI-DSS, or CCPA compliance.
Performance Impact: Some encryption methods may slow down system performance—test before deployment.
Scalability: Choose a tool that grows with your organization’s security needs.
Integration: Ensure compatibility with existing cloud, database, and network infrastructure.
Step-by-Step Guide to Implementing Data Encryption
Implementing data encryption effectively requires a structured approach to ensure security while maintaining usability and compliance. Below is a step-by-step guide to deploying encryption successfully in your organization.
Step 1: Identify Data That Needs Encryption
Conduct a data classification assessment to determine which data is sensitive and requires encryption.
Focus on personally identifiable information (PII), financial records, intellectual property, and regulatory-sensitive data.
Map out where this data resides (e.g., databases, cloud storage, employee devices, emails).
Tip: Not all data requires encryption—prioritize protecting high-value and high-risk information first.
Caution: Encrypting everything indiscriminately may lead to unnecessary system overhead and performance degradation.
Step 2: Choose the Right Encryption Algorithm
Select a strong encryption algorithm based on data type and regulatory requirements:
AES-256: Ideal for file encryption, full-disk encryption, and cloud data security.
RSA-2048+ or ECC: Suitable for public-key encryption in SSL/TLS communications.
SHA-256 or SHA-512: Used for password hashing and ensuring data integrity.
Verify that the encryption method complies with GDPR, HIPAA, PCI-DSS, or other industry regulations.
Tip: AES-256 is widely accepted as the gold standard for securing sensitive data.
Caution: Avoid outdated encryption methods like MD5, DES, or SHA-1, as they are considered insecure.
Step 3: Secure Encryption Keys
Store encryption keys in separate, secure environments rather than alongside encrypted data.
Use Hardware Security Modules (HSMs) or cloud-based key management services (AWS KMS, Google Cloud KMS) for centralized control.
Implement automatic key rotation policies to prevent key exposure over time.
Restrict access to encryption keys using role-based access control (RBAC) and multi-factor authentication (MFA).
Tip: Encrypt your encryption keys themselves with a master key for an extra layer of security.
Caution: Poor key management can lead to data loss—if the key is lost, the data becomes permanently inaccessible.
Step 4: Encrypt Data at Rest, In Transit, and In Use
Data at Rest: Encrypt stored files, databases, and backup archives.
Use full-disk encryption (FDE) for laptops and servers.
Implement database-level encryption for structured data storage.
Data in Transit: Secure communication channels with SSL/TLS encryption.
Enable email encryption for sensitive correspondence.
Use VPNs for secure remote access.
Data in Use: Protect data being actively processed in applications.
Utilize memory encryption techniques to guard against live data breaches.
Restrict temporary file storage to prevent leaks.
Tip: Implement end-to-end encryption (E2EE) where possible to ensure complete data protection.
Caution: Unencrypted backups are a common vulnerability—ensure that all stored data is encrypted.
Step 5: Enforce Strong Authentication and Access Controls
Implement multi-factor authentication (MFA) for users accessing encrypted data.
Use zero-trust security models that require identity verification before granting access.
Configure least-privilege access controls, allowing only necessary personnel to access sensitive data.
Tip: Monitor access logs and set up real-time alerts for unauthorized access attempts.
Caution: Weak authentication undermines encryption—compromised credentials can lead to data exposure.
Step 6: Regularly Update and Patch Encryption Systems
Keep encryption software and firmware updated to protect against vulnerabilities.
Apply patches immediately when vendors release security updates.
Use automated update tools to ensure timely deployment of security fixes.
Tip: Subscribe to CVE (Common Vulnerabilities and Exposures) databases to stay informed about encryption-related threats.
Caution: Outdated encryption software is a major attack vector—ensure updates are applied consistently.
Step 7: Monitor and Audit Encryption Implementations
Use SIEM (Security Information and Event Management) tools to track encryption activity and anomalies.
Conduct regular security audits and penetration tests to assess encryption effectiveness.
Generate compliance reports for regulatory audits and internal governance.
Tip: Automate compliance monitoring with security frameworks like NIST, CIS Controls, and ISO 27001.
Caution: Failure to audit encryption implementations can lead to undetected weaknesses and security gaps.
Step 8: Educate Employees on Encryption Best Practices
Train staff on data protection policies and proper encryption usage.
Raise awareness about phishing attacks and social engineering that could compromise encrypted data.
Establish a clear incident response plan in case of encryption key loss or a data breach.
Tip: Simulate security incidents with tabletop exercises to prepare employees for real-world cyber threats.
Caution: Human error remains one of the biggest security risks—regular training is essential.
Final Thought
Implementing data encryption is a multi-faceted process that requires careful planning, strong key management, continuous monitoring, and regular updates. By following these best practices, businesses can significantly reduce the risk of data breaches, ensure compliance with security regulations, and maintain customer trust.
Next Steps:
Conduct an encryption risk assessment, identify critical data for encryption, and begin implementing security controls tailored to your organization’s needs.
Follow these steps to successfully implement encryption in your organization:
Step 1: Identify Data That Needs Encryption
Prioritize sensitive data such as customer records, financial transactions, passwords, and intellectual property.
Classify data based on risk level.
Tip: Not all data requires encryption—focus on protecting high-value information.
Step 2: Choose the Right Encryption Algorithm
Use AES-256 for most applications (widely regarded as unbreakable).
For web communications, implement TLS encryption.
Use RSA or ECC for public-key cryptography.
Caution: Avoid outdated encryption methods like MD5 and DES, which are no longer secure.
Step 3: Secure Encryption Keys
Store encryption keys separately from encrypted data.
Use hardware security modules (HSMs) for key management.
Rotate encryption keys regularly to prevent compromise.
Tip: Implement role-based access control (RBAC) to limit who can access encryption keys.
Step 4: Encrypt Data at Rest, In Transit, and In Use
At Rest: Encrypt files stored on hard drives and cloud servers.
In Transit: Use SSL/TLS for secure web and email communications.
In Use: Implement real-time encryption for data actively being processed.
Caution: Unencrypted backups can be a security risk—ensure backup data is encrypted as well.
Step 5: Test and Audit Encryption Regularly
Conduct penetration testing to identify weaknesses in encryption implementations.
Monitor encryption logs for unusual activity.
Stay updated on encryption standards and vulnerabilities.
Tip: Use automated tools to track encryption compliance and security performance.